What IS authentication?
Authentication, at its core is about validating someone’s identity. To execute a transaction, like withdrawing cash, interacting with a trusted system, or even entering a building. Most of us use some sort of authentication service every day. We are accustomed to this, as we use our face to unlock our iPhones or SMS, and use email verification to log in to our various accounts.
The standard mechanism of authentication that the majority of people are familiar with is the use of passwords. So a password is one factor to protect something of value. However, having an increasingly tricky password becomes unwieldy for the user. But to protect valuable assets from being hacked or compromised, a second Factor (2FA) is needed. Sometimes, we need even more factors, making it Multi-Factor Authentication (MFA).
Why is 2FA and MFA needed?
Let’s use a specific example. You have a bank account with your hard-earned money in it, and your bank has a website or application for access. To log in, you can enter your username and password, but you’ve recently learned that your bank had a data breach, and your information might now be available to hackers.
You can do nothing and run the risk of a stranger accessing your account, or you can set up 2FA. Now, anytime the account is accessed, it requires you to verify your identity through something you know or something you have with you (the 2FA). The chances of someone having access to both factors are slim, thus increasing the security of your bank account.
So what is 2FFA?
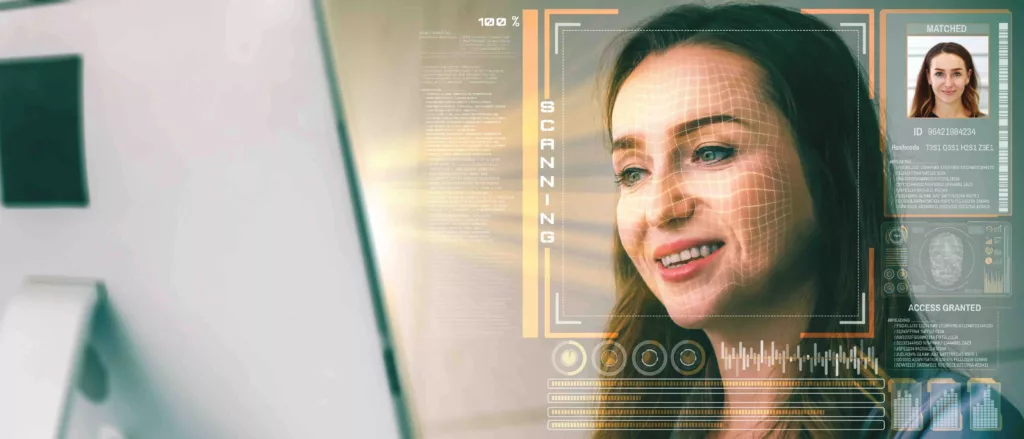
A special case of 2FA is 2FFA, or second Factor of Facial Authentication (2FFA). Your face is something you have and carry around with you. Using your face as your second factor is very prudent and secure. Passwords can be cracked with compute, and keycards can be compromised or passed around, diminishing authentication. Your face is a highest secure authentication mechanism.
When people use our facial authentication software, they’re opting in to use their face as their unique form of identification. Wicket’s software is often used as 2FFA by customers that already have traditional security mechanisms (such as a keycard or lock-and-key) and also want to add security (or extra factor). Increasingly, customers use facial authentication as a primary factor, or the only security. Especially when controlling physical access into a restricted area or space.
By pairing Wicket’s facial authentication products with existing access control hardware, our customers can rest assured knowing that they have two or even three layers of authentication in place to protect their most valuable areas or assets.